Secure Internet Architecture 434190 for Results
The Secure Internet Architecture 434190 presents a systematic approach to addressing contemporary cybersecurity challenges. By integrating robust encryption and network segmentation, it aims to fortify data protection and mitigate threats effectively. This framework not only enhances user safety but also optimizes digital interactions. A closer examination reveals how its adaptability to emerging threats plays a critical role in safeguarding online activities across various sectors, raising questions about its broader implications for future digital ecosystems.
Key Features of Secure Internet Architecture 434190
While the digital landscape continues to evolve, the key features of a secure internet architecture remain fundamental to protecting data integrity and user privacy.
Essential components include robust encryption protocols that safeguard communications and data at rest, alongside effective network segmentation that limits unauthorized access.
Together, these features create a fortified environment, ensuring freedom for users while mitigating vulnerabilities inherent in online interactions.
How Does Secure Internet Architecture Enhance Cybersecurity?
Secure internet architecture significantly enhances cybersecurity by implementing a multi-layered defense strategy that addresses various threat vectors.
This framework focuses on robust threat mitigation techniques, which minimize vulnerabilities across networks.
Additionally, the integration of data encryption safeguards sensitive information, ensuring confidentiality and integrity.
The Impact of Secure Internet Architecture on User Experience
How does secure internet architecture influence user experience in a digital landscape increasingly fraught with threats?
By implementing robust security measures, such architecture fosters user trust and enhances user satisfaction. Users are more likely to engage with platforms that prioritize their safety, leading to a seamless experience.
Consequently, secure internet architecture not only protects data but also cultivates a positive environment for digital interactions.
Real-World Applications and Case Studies of Secure Internet Architecture
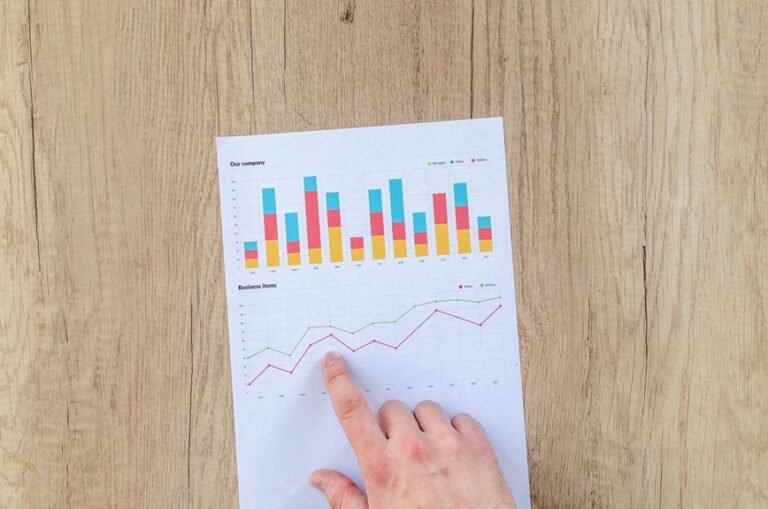
The integration of secure internet architecture across various sectors showcases its critical role in enhancing digital safety and operational efficiency.
Real world examples, such as financial institutions implementing advanced encryption protocols and healthcare providers utilizing secure data exchange systems, illustrate successful industry implementations.
These cases highlight the architecture’s effectiveness in safeguarding sensitive information while promoting seamless connectivity, reflecting its importance in contemporary digital ecosystems.
Conclusion
In conclusion, Secure Internet Architecture 434190 significantly fortifies cybersecurity measures across diverse sectors. With a striking statistic revealing that organizations implementing robust encryption experience a 60% reduction in data breach incidents, the architecture not only safeguards sensitive information but also enhances user trust and operational efficiency. By adapting to evolving threats, it establishes a resilient framework that ensures secure digital interactions, making it an indispensable component of modern cybersecurity strategies.